The totality services blog
Lessons From the CTS CitrixBleed Attack
A massive cybersecurity crisis happened in November 2023 when CTS, a UK-managed service provider (MSP), was affected by the CitrixBleed …
Digital Transformation: Technology Grants For Nonprofit Organisations
Technology lets nonprofits improve their communication strategies and service delivery, but high prices often act as a barrier. Fortunately, technology …
How to Use Microsoft Copilot: A Guide for SMBs
If you’re steering a small or medium-sized business (SMB) and looking for ways to simplify your daily tasks, then Microsoft …
Microsoft Dynamics 365: How to unlock the potential
Microsoft Dynamics 365, formerly known as Microsoft Dynamics CRM, has a lot to offer to businesses in a wide range …
What are the different levels of IT support? (explained)
IT support is an umbrella term that refers to any type of assistance with technical issues. To segment and streamline …
What is IT support? (Comprehensive guide for businesses)
IT support is a broad term that refers to technical support relating to issues concerning your company’s tech infrastructure. This could …
More blog
Ransomware attacking businesses around the world
The year of 2016 and 2017 was impactful in the technological world with the appearance of Ransomware attacking businesses. WannaCry and Petya cyber attacks had rocked the world, sending governments into a tizzy, businessmen scurrying …
5 steps for Optimising Your VPN Experience
A VPN services is essential to remaining safe when working remotely, although it’s important that once set up, you learn how to proactively optimise it in order to boost your performance. A Virtual Private Network will encrypt your network traffic, preventing others from viewing intercepted data.
How to share and publish your Outlook calendar
How to share and publish your Outlook calendar We are often asked by our London based IT clients how they …
Everything you need to know about Malware attacks
Malware attacks ‘Malware’ or malicious software is a term that describes any malicious program or code referring to a variety …
How to protect data on your Employees’ Devices
To avoid problems related to data security on employee devices, BYOD policies must be established and reinforced regularly. Here’s how you, as a business owner, can protect data on your employees’ devices.
Tips to Protect Your Business from Cyber Attacks
Protect Your Business from Cyber Attacks The internet has opened doors to new opportunities for businesses. Thanks to the internet, …
Cybersecurity practices that all small businesses should follow
Best cybersecurity practices Many small business owners do not consider cybercrime a threat. They often assume that if they believe they …
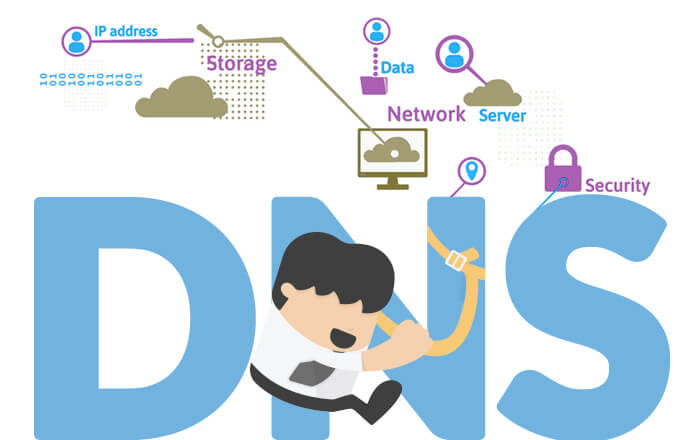
All You Wanted to Know About Domain Name System Protection
Domain Name System Protection When the internet was introduced, there were very few systems and services connected to the network. …